1.
Application Structure
The Oracle
E-Business Suite (EBS) Enterprise Resource Planning (ERP) system is an
integrated software solution that runs off an Oracle database instance. An ERP
consists of applications or “modules”. Most modules hold transactional data for
each business process area (financials, supply chain management, customer
relationship management, manufacturing, human resources, etc.). Some modules
are used for system-wide support. Each module is linked to each other via the
database; therefore, information is seamlessly integrated.
Users
access functions either via a forms-based model, or in the case of Self-Service
modules, a web-based model via the End User Tier mentioned in further detail
below.
The Oracle EBS
system is a three-tier system that consists of the End Users Desktop,
Application Servers and Database Servers.
1.1. End User Tier
The end user tier is the path by which
users gain access to the application tier. Users access the application via their
own computers and a URL address. From the URL address, users enter a user name
and password (previously defined at the application tier), which grants them
access to the application tier. Once onto the application tier, user access is
governed by responsibilities assigned to the user.
1.2.
Application Tier
The application layer, or middleware,
contains the key application programs as well as programs to support web use,
screens and administrative tasks within the system. There are several key
servers that may exist within this layer some of which are detailed below:
1.2.1. Web Server
(Oracle Portal)
The Portal manages
access to Oracle ‘Forms’ (note that this is the definition Oracle uses to
describe screens or windows displayed on the monitor).
1.2.2. Forms Server
The forms server
stores the format of the Oracle forms. This is also where the application and
some administrative functions reside (i.e. entering and posting of journal
entries). The forms server interfaces directly to the Database tier.
1.2.3. Concurrent
Processing
The Concurrent
Processing's primary purpose is to load balance the system and enhance
performance. Concurrent processing is managed through a scheduling system that
controls when updates occur. Along with the scheduling system, concurrent
processing can prioritize activities based on transaction importance. It is
also used to provide batch processing capability.
Reports and other
requests are executed by this server, which interfaces directly to the Database
tier.
1.2.4. Administration
Server
This server
interfaces directly to the Database tier and provides operational support such
as backup, recovery, startup and shutdown. In addition, it provides statistical
information on system use and performance.
1.3.
Database Tier
The database environment allows for storage
and retrieval of user and administrative data and of other application programs
and components. Oracle Enterprise Database Management System (DBMS) is the only
DBMS that will work with Oracle applications. Releases of Oracle DBMS are
intended to operate with specific versions of Oracle applications. The version
numbers of the database do not correspond with the Oracle applications version
numbers. Within Oracle EBS, all data (master, standing, security and transactional)
are stored in the Oracle DBMS.
Since the Oracle DBMS contains all
Oracle-related financially-significant data, the Oracle DBMS is considered the
highest risk of the three tiers.
1.4. File System
Oracle has made a
primary change to the file structure supporting the applications in Release 12.
Oracle has now provided an instance-specific directory(s) to support each
unique environment - dev, test, prod, etc. The new instance home model
supports two key concepts:
·
The
base configuration directories APPL_TOP and ORACLE_HOME can be read-only to
support change control. With instance-specific data files separated into
dedicated directories, upgrades and migrations should be more easily
controlled. Common application files are not touched for instance-specific
modifications.
·
Another
advantage of employing the concept of an Instance Home is that log files can be
stored centrally for an instance, and therefore managed more easily. This is
particularly significant from a security perspective, as log files may contain
sensitive data that should not be accessible to general users.
The following picture depicts the structure
of the Oracle EBS file system:
2.
Oracle Application Release History
|
Version
|
Release date
|
Market Prevalence
|
Functionality Changes
|
Practice Aid and Work Program Applicability
|
|
10.7
|
1998
|
-Rare.
-Limited support by Oracle corporation.
|
-Limited system audit capabilities
-Full character based
|
No
|
|
11.0.3
|
1999
|
-Limited.
-Full support by Oracle.
|
-Corrected Y2K deficiencies
-Included client / server environment
-Introduced GUI Interface
|
No
|
|
11.5.5, 11.5.6
|
2000
|
-Limited Use
-Supported by Oracle
|
-Enhanced performance
-Web based
|
Yes
|
|
11.5.7, 11.5.8, 11.5.9
|
2002 (5.7)
|
-11.5.7 & 5.9 in broad use
-11.5.8 use limited (buggy)
|
-Expansion in Web based and workflow functionality
|
Yes
|
|
11.5.10
|
2005
|
Broad use
|
-Significant changes in System Administration
module, including limited introduction of Role Based Access Control.
|
Yes
|
|
12
|
2007
|
Latest release.
|
-Significant changes in System Administration
module, General Ledger, and infrastructure.
|
Yes
|
3. Overview of
System Administration
The Application
Object Library (AOL) module is the gateway to all functionality in Oracle applications. The following key functions
are performed within the AOL module:
·
Flexfields
·
Auditing and Change
Control
·
User Management
·
System Profile
Options
·
System Reports
NOTE: Internally at
PwC, we refer to the AOL and System Administration module together as System
Administration (SA).
3.1. Flexfields
As
the name suggests, flexfields are flexible fields made up of sub-fields, or
segments. Oracle uses two types of flexfields: key flexfields and descriptive
flexfields. Key flexfields are stored codes (or values) used system-wide for
general ledger accounts, part numbers, and other business entities. On the
other hand, Descriptive flexfields provide customizable "expansion
space" on Oracle forms to track unique to the company's business. For a
more detailed discussion of flexfields, refer to the Flexfields section below.
3.2. Auditing
and Change Control
Auditing
can be enabled to monitor changes made either through the application or
directly to the database rows. In addition, the application can be
enabled to monitor successful and unsuccessful user logons and the
responsibilities, terminals, or forms accessed by a user are noted.
Change
control monitors who requested the change, the expected results from the
change, the testing procedures and their outcomes, and the final approval by
management to implement the change in production. A record of change
control includes who, what, when, where and why. Please see the Auditing
section of this Practice Aid for further discussion.
The
iSetup functionality available from 11i can support the change management
process. It enables administrators to extract, transform and migrate setup data
in a controlled way and compare setup data with available standard reports.
3.3.
User Management
In
addition to the AOL module, the System Administration module is used to store
the Oracle responsibility (user profile) definitions. There are various
objects/settings assigned to a responsibility within the application that allow
a User ID the ability to perform activities within Oracle (i.e. data groups,
menus, functions and request security groups). The application comes with a
number of default responsibilities, but a company can customize
responsibilities to suit their business needs and restrict access to various
tasks as appropriate.
Responsibilities can be defined to allow access to the following areas:
·
Specific
applications/modules.
·
Ledger name/Legal
entity.
·
Restricted list of
windows.
·
Restricted list of
functions.
·
Reports in specific
application.
A diagram outlining the relationship between users, responsibilities,
functions and modules is below:
There is no default user access that is granted just by being given an
account in Oracle EBS. The security administrator (through the System
Administrator responsibility) must assign a User ID with responsibilities for
the user to be granted abilities to perform tasks/functions within Oracle.
Due to the newly introduced functionality multi-organizational access
control (MOAC)
functionality, users can access multiple operating unit (OU) data either within
or across business groups from a single responsibility. Using MOAC, multiple
operating units are assigned to a security profile. This security profile is
then assigned either to responsibilities or directly to users. A typical usage
would be responsibility in a shared service centre, which serves different
operating units. For further details on MOAC please refer to the section on
Multiple Organization Access Control.
3.4. System Profile Options
System Profile Options can be grouped into three types: Security,
Organization, and Server types. Practitioners are mainly concerned with
Security type profile options that affect the operation of Oracle Applications.
Security type profile options can be configured according to the needs of the
user community, as they can be set at the Site, Application, Responsibility, or
User level. Security profile options are generally maintained by the
Application System Administrators and may be set at more than one level: Site
has the lowest priority, superseded by Application, then Responsibility, and
finally User. Higher profile option settings will override lower level options.
The security system profile options hierarchy is documented below in the
diagram. Please see the System Profile Options section of this Practice
Aid for more details.
3.5. System Reports
The following table lists key default reports that can be used for
the assessment of Oracle System Administration when the Oracle GATE Application
is not being utilized:
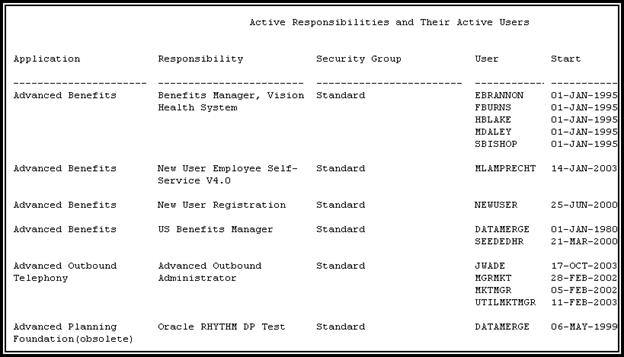
|
Reports
|
Description
|
|
Active Responsibilities and Users (Application
Object Library)
|
The report of responsibilities linked to the users
assigned to the responsibility
|
|
Active Users
|
All the usernames that are both currently active and
have at least one active responsibilities
|
|
CP SQL*Plus Expire FND_USER Passwords
|
Concurrent Request to Force All Applications Users
To Change their Password
|
|
Workflow Directory Services User/Role Validation
(Application Object Library)
|
Validates the user/role information in Workflow
Directory Services
|
Sample report: Active Responsibilities and Users
Report






 Get Flower Effect
Get Flower Effect
No comments:
Post a Comment